Meta Backs Away After Mercor Confirms Major Breach via LiteLLM Supply Chain Attack

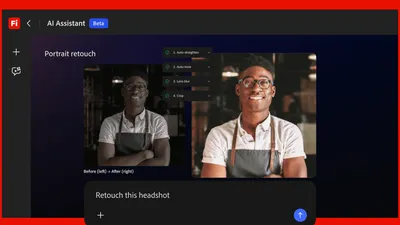
Image: TechCrunch AI
Main Takeaway
Meta halts Mercor data deals as $10B AI provider admits LiteLLM breach; OpenAI and Anthropic still assessing fallout.
Summary
The breach at a glance
Mercor, the $10 billion AI recruiting startup that feeds expert-labeled training data to OpenAI, Anthropic, and Meta, has confirmed it was breached through the compromised open-source LiteLLM project. The company told TechCrunch it was “one of thousands” hit. Now Wired AI reports that Meta has frozen all new data purchases while it investigates whether proprietary prompts and model-training secrets leaked.
How the attack unfolded
LiteLLM is a lightweight proxy library that lets developers route prompts to dozens of large-language-model providers with one line of code. Attackers slipped malicious code into a late-March release, then waited for downstream users to ingest it. Fortune says Mercor’s build systems pulled the poisoned package, giving intruders a foothold they later escalated. Mercor spotted the intrusion on April 1 and yanked LiteLLM the same day.
What data may be at risk
Dark-web posts seen by Cybernews brag about 4 TB of “critical” Mercor data: proprietary interview recordings, candidate PII, and expert-labeled prompt-completion pairs from medicine, law, and finance. Because Mercor’s customers pipe those datasets straight into model fine-tuning, any leak could expose trade-secret prompts or copyrighted material. Mercor hasn’t confirmed the 4 TB figure but has begun notifying partners under breach statutes.
Meta pulls the plug
Wired AI reports that Meta has “paused work” with Mercor while it audits what, if anything, crossed into its training pipelines. The freeze covers new data purchases and existing evaluation datasets. OpenAI and Anthropic are still assessing exposure; neither has changed its relationship status yet. For Meta, the move is immediate risk management—its Llama family of models relies heavily on third-party data vendors, and any contamination could force costly retraining.
Ripple effects across AI land
Smaller labs that license Meta’s models are watching closely. If Meta rewrites contracts or demands stricter audits, the entire data-labeling industry could face new compliance hurdles. Meanwhile, LiteLLM’s maintainers have rolled back the malicious release and published a timeline, but trust has already cratered. GitHub stars are dropping, and several startups have forked the repo to self-host sanitized versions.
What happens next
Mercor has hired CrowdStrike for incident response and promised a public post-mortem within 30 days. Meta’s freeze lasts “until we understand the blast radius,” a spokesperson told Wired AI. OpenAI and Anthropic haven’t set deadlines, but people close to both companies say internal red teams are stress-testing recent model updates for anomalies. If any dataset turns out tainted, retraining costs could climb into the millions—pocket change for giants, lethal for smaller players.
Key Points
Meta has formally paused all new data purchases from Mercor while it audits exposure.
Mercor confirmed attackers used a poisoned LiteLLM release to gain access in late March.
Up to 4 TB of proprietary AI training data, including expert-labeled prompts, may have leaked.
OpenAI and Anthropic are still assessing risk; neither has changed vendor relationships yet.
LiteLLM maintainers rolled back the malicious release, but repo trust is in free fall.
FAQs
No. Meta has only paused new data purchases and evaluations while it investigates; the freeze is temporary.
Dark-web posts claim 4 TB of data includes candidate PII, but Mercor hasn’t confirmed the scope.
Yes. Both companies are conducting internal reviews but haven’t altered their contracts yet.
Source Reliability
33% of sources are trusted · Avg reliability: 63
Go deeper with Organic Intel
Our AI for Your Business systems give you practical, step-by-step guides based on stories like this.
Explore ai for your business systems